
Your Strategy for Shadow IT Sourcing
Wait a moment, does it actually make sense to talk about shadow IT and sourcing strategy in the same breath?

Wait a moment, does it actually make sense to talk about shadow IT and sourcing strategy in the same breath?
If you’ve archived backups of data for contractual or regulatory reasons, do you also need to back that data up?

There is some deeper relationship between IT security and the sea that has yet to be fathomed.
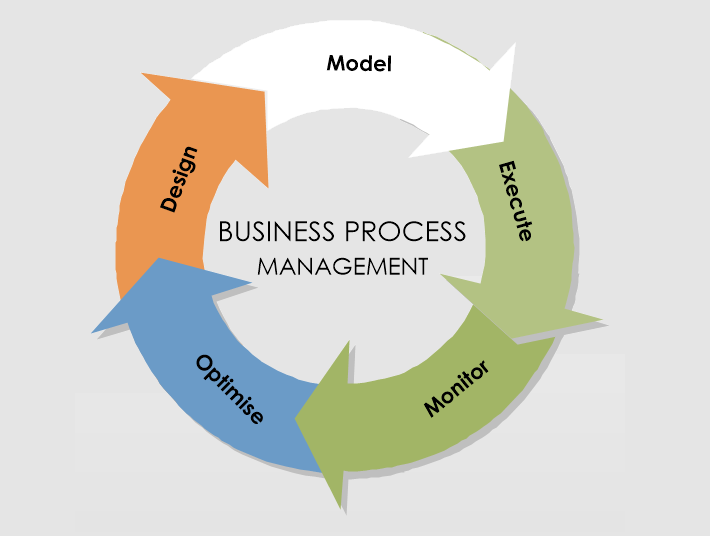
Take IT as a service, IT governance and maybe some business process execution language, and mix them all together.

People and organisations generate more data than ever before. Smart software can analyse mountains of data and offer insights and recommendations, or even take decisions.
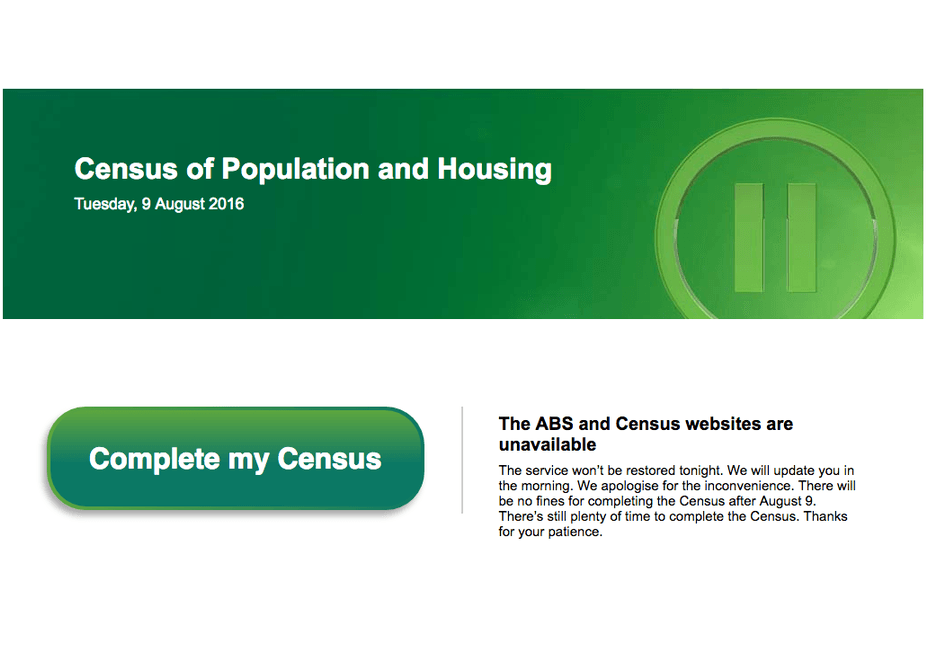
What were Australian’s doing on the evening of the 9th of August, 2016? All jumping on the bandwagon to fill out their Australian Bureau of Statistics (ABS) Census details on the Census website.
If you’ve met blockchain before, it may well have been in the context of the cyber currency Bitcoin.
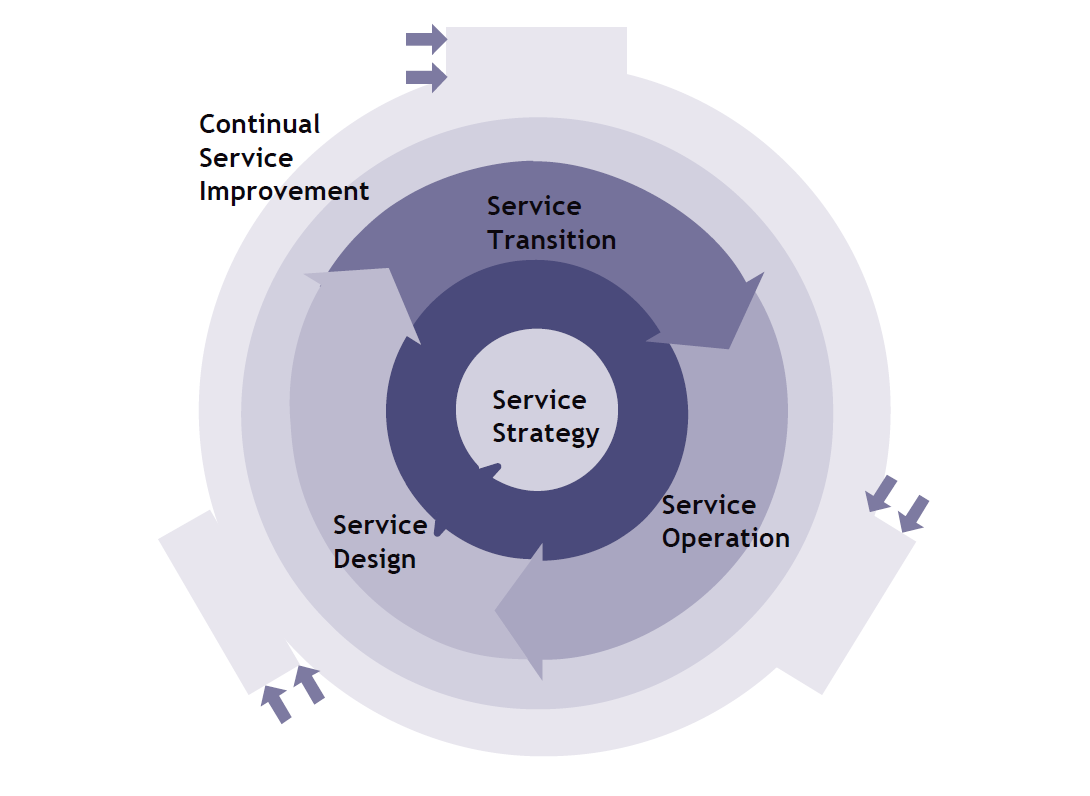
What do ITIL and DevOps have in common, you may ask – apart from the syllable “Ops”? So far these two items have had little overlap, but that may now start to change significantly.

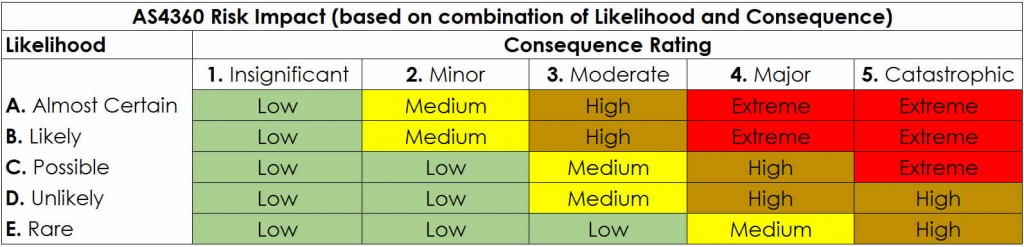
In business risk management, risk-reward is a concept known by many, but understood by rather fewer.
Enterprises can come up with all sorts of schemes for cutting waste and costs, ranging from cancelling coffee machines to selling off entire business units.

A survey showed that commuters in London more often than not (more than 70%) would reveal their computer password in exchange for a bar of chocolate.
Now that business apps (that really can help you do better business) are available immediately in the cloud, the internal IT organisation may find itself being ignored as the shadow IT.

What would you expect residents of Sydney to be doing Sunday afternoon and evening, 5 June 2016?
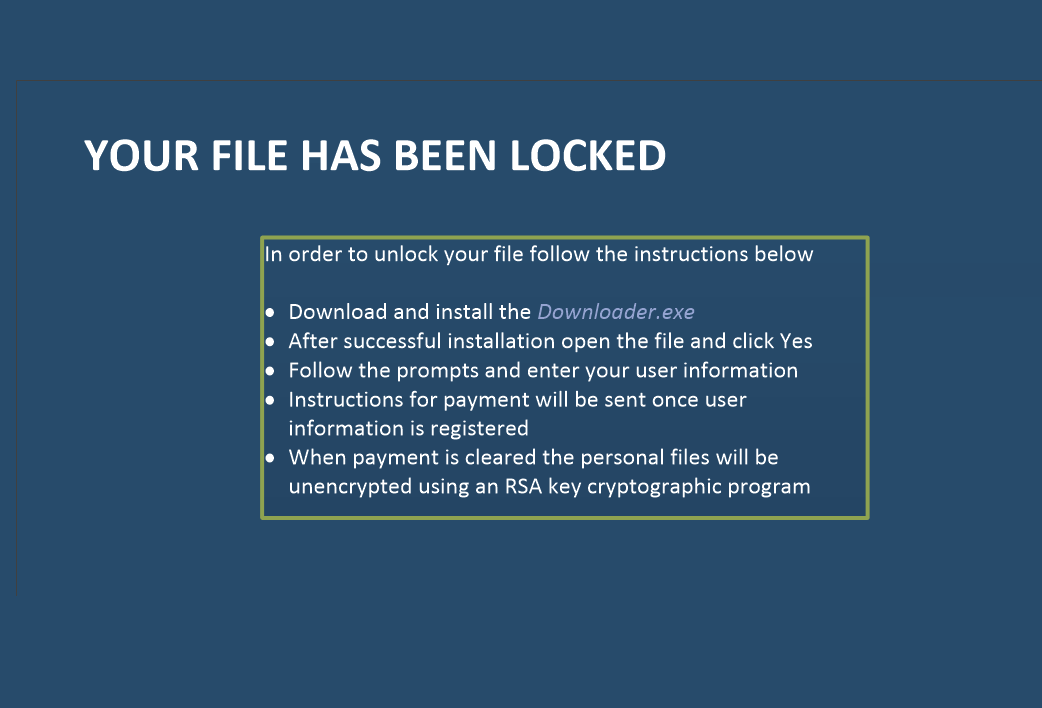
It would be risky to generalise from one specific example in IT security, but the case of fake ransomware is intriguing.

Supply Chain Resilience have so many moving parts that rapidly becomes a priority issue.

In business continuity planning, business impact analysis or BIA is possibly the most critical part.
Let’s be honest. Between ‘Risk Evaluation’ and ‘The Science of Danger’, the second name has more star quality.

Where do cyber criminals focus their attacks? On the organisations with the information of most interest or highest worth, naturally enough.

As IT morphs from legacy on-site systems and firewalls to cloud computing, mobility and data-anywhere, it is having to change in terms of agility and security.

Looking at how other enterprises organise their business continuity can be beneficial for two reasons. First, it helps to compare your own preparations with those of another entity.

IT Security perimeters no longer exists, now that mobile and cloud computing are so prevalent. The availability of files and information to employees in the office, on site, on the road or at home is high.

Remember the economic meltdown (almost) of eight years ago? Two buzzwords came to the fore at that time. One was “systemic risk”, the risk that applies to an entire sector or domain; in this case, the global economy.

Often, techniques that are invented in one domain can be of use in another one too. If you’ve spent your working in life so far in business continuity, you may not have seen much of the lean approach that is frequently used in manufacturing.

The company has a vision of making its Messenger app the default communication mode for businesses, whether with other businesses or with customers.

On the face of it, business continuity is a robust process. You gather the appropriate information, apply methodologies to assess business risk.

It is easy to indulge in navel-gazing when it comes to business continuity. We examine your business, its components, its requirements, its objectives and the risks that could affect it.

A Local Resilience Forum? Should you have one? Also referred to for short as an LRF, the idea is to bring together different respondents in a local area in order to guarantee cooperation

Current press coverage may be focusing on exaflops and artificial intelligence, but the IT success story of the decade is still likely to be cloud computing as Cloud Business Continuity struggles to bring much progress.

Smart mobile has so far been largely a consumer-driven market. That has been good news for the business sector. It has reaped the benefits of the technological advances and better user experiences, with which vendors have sought to woo Jane and Joe Public.

Willie Sutton was the man who (according to a popular story) gave the definitive answer to the question “Why do you rob banks?” He said “Because that’s where the money is”.
Get Started
For urgent inquiries, call us on 1300-BCPLAN (Intl. +612 9098 9000)



As an executive in any business, it is understandable that you want to ensure it is 100% safe, because your business is only as strong as its weakest link.
+612 9098 9000
subscribe our newsletter go get the latest updates and news from Opscentre
Copyrights © 2024 OpsCentre | Powered by PixxelStudio86.