
Why IT Strategy Fails and What to Do About It
IT strategy – hmm, that sounds good! It suggests you know what you’re doing, and that those invoices from your IT suppliers correspond to something of value to the business.

IT strategy – hmm, that sounds good! It suggests you know what you’re doing, and that those invoices from your IT suppliers correspond to something of value to the business.

We know you know, but to save you the mental effort of fleshing these acronyms out into full-length descriptions, here’s what they stand for. BCM is business continuity management. ITSCM is IT service continuity management.
Paved with good intentions and best practices, the road to ITIL hell can look so alluring to the unwary IT manager.

Can these two items coexist? Business continuity is about keeping things going, whereas business transformation is often about breaking things (figuratively, if not literally) to get out of a rut and into a new, more competitive mode of business.

5G networks is on the horizon now, destined to increase mobile data transfer speeds and reduce communications latency compared to current 4G.
IT servers, enterprise applications, data centres and cloud services might seem world away from other sectors traditionally attracting attention in terms of a ethical sourcing strategy.

Start humming the James Bond theme, now. Or perhaps not. Agents in IT asset management don’t quite have the glamour of 007.
The advanced persistent threat or APT is the up and coming menace to IT systems today.

The road to IT sourcing nirvana is full of potholes, not to mention the ravines on either side, should you stray from the straight and narrow.

Now and again, we hear rumblings about IT governance and how synergy must be developed between IT and the rest of the organisation to work in harmony as a “business partner”. The principles are praiseworthy.
The man in question is Nassim N. Taleb. He coined the term “Black Swan” in risk management to describe events that are unforeseeable, even highly unlikely, yet that happen and in doing so change the course of history.

According to some sources, only 10% of any business strategy plans are ever effectively implemented.

As free and freely available software that has helped millions of individuals and enterprises easily establish a presence on the web, WordPress has a reputation for being well-designed and reliable.

You mean, there is one? Yes, indeed – You see, online dating organizations are all about asset relationships, preferences, likes and dislikes.
Hooray for World Backup Day, you might think, reminding people how important it is to safeguard data and systems.

A well-paid, but heavy responsibility with a built-in ejector seat is one way of looking at the CISO position.
You’d be surprised at the emotional bonding that can go on between users and their IT hardware devices but there’s a difference between managing your asset appropriately and actually collecting a heap of junk hardware you’ll never use.
How do you measure your IT service success and failure? Performance numbers and metrics can be valuable, because they help you to improve, as well as to defend your IT service management against possible criticism.
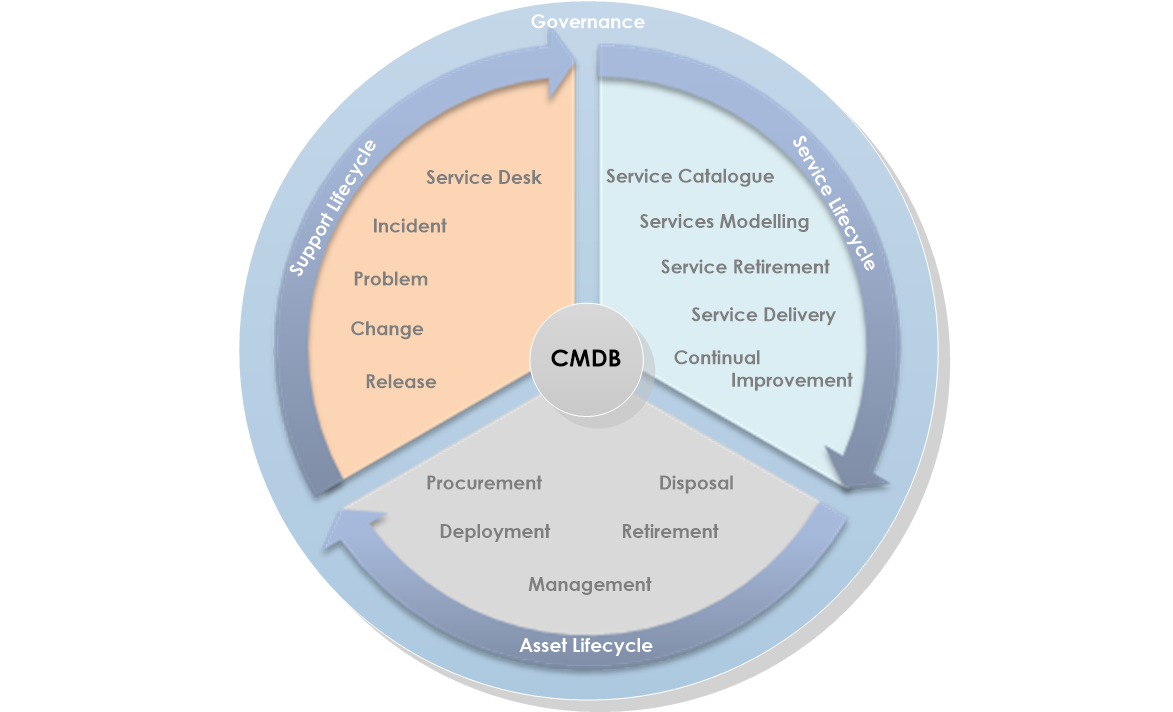
Enough of the four-letter acronyms! CMDB, in case this had slipped your memory, stands for configuration management database.
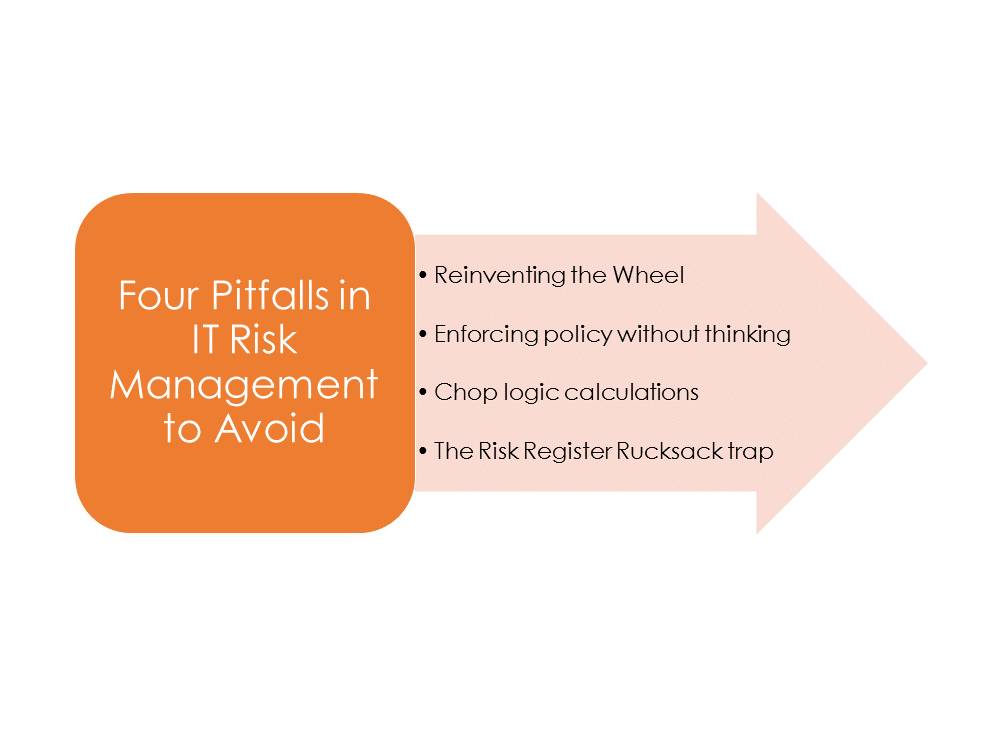
IT risk management can be a risk all by itself. Although the principles sound straightforward, applying them incorrectly can lead to wasted effort, mistakes in risk postures, and failing to spot relevant risks or changes in those risks.

Don’t worry, all you IT people, you won’t lose your jobs because IT service management changes its name.
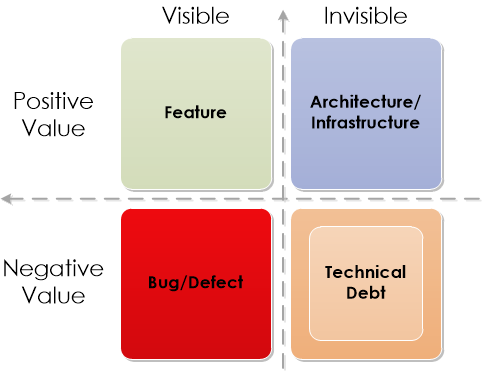
When you shove things higgledy-piggledy into your desk drawer, just to clear space in your workspace, you have a quick solution, you also have a dirty solution, because trying to find the key to your filing cabinet will take you ages afterwards, and Yes, you’ve just experienced technical debt, first hand!

IT risk management is a common thread running through IT investments, IT security, IT disaster recovery, and business continuity.

If ain’t broke, don’t fix it, as the saying goes. However, even unbroken IT installations must be fixed by patches, upgrades or redesigns to meet new business objectives. ITIL Problem Management Processes tackles the issue by taking a problem-solving and root cause approach.

This is a little like asking “how long is a piece of string”, except that in this case the string may already be a lot shorter than you imagined. Passwords are often the bane of the IT helpdesk.
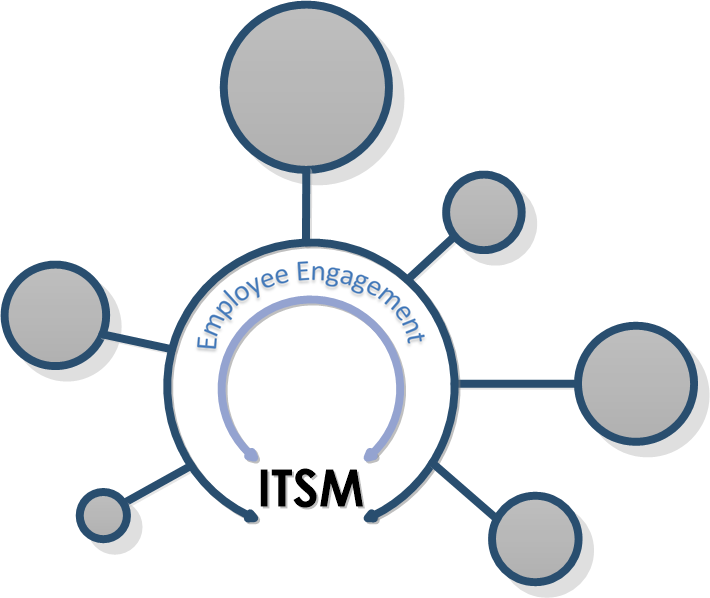
Does talking about these items in the same breath seem incongruous to you? After all, IT service management is typically viewed as technology at the service of an enterprise and its end-users, helping productivity, rather than being linked directly with motivation.

So much of business is being scrutinized through the lens of uberisation that it would be an omission (and possibly a dangerous one) to neglect a quick squint at business continuity.

Sure, as a CIO or IT manager, you know what IT risk management is. It’s all about applying risk management principles to IT, including the adoption, ownership, operation and influence of IT within the larger context of the enterprise but in terms of risk management language, are these principles communicated properly across the organisation?
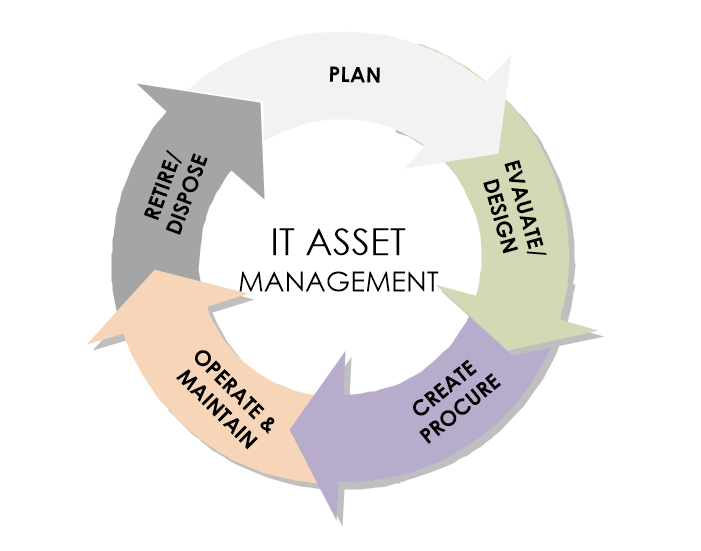
“Here, take my old PC. I’m getting a new one to help meet my advanced needs, but this one will surely do the job for you.” This, in a nutshell, is cascading in IT asset management.

On the face of it, it sounds simple. IT strategy should be driven by business requirements.
Get Started
For urgent inquiries, call us on 1300-BCPLAN (Intl. +612 9098 9000)



As an executive in any business, it is understandable that you want to ensure it is 100% safe, because your business is only as strong as its weakest link.
+612 9098 9000
subscribe our newsletter go get the latest updates and news from Opscentre
Copyrights © 2024 OpsCentre | Powered by PixxelStudio86.